Investors Allege Cybersecurity Assurances Masked a Persistent Breach
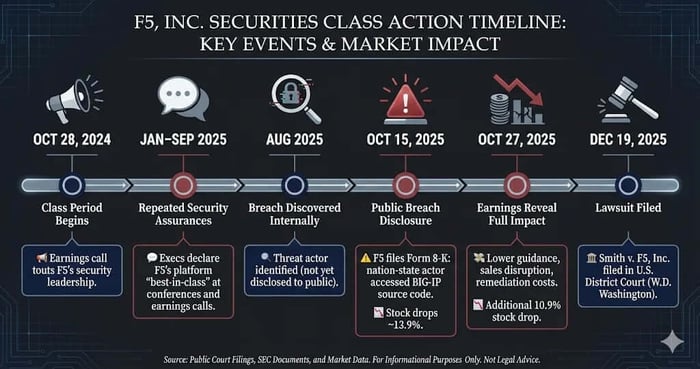
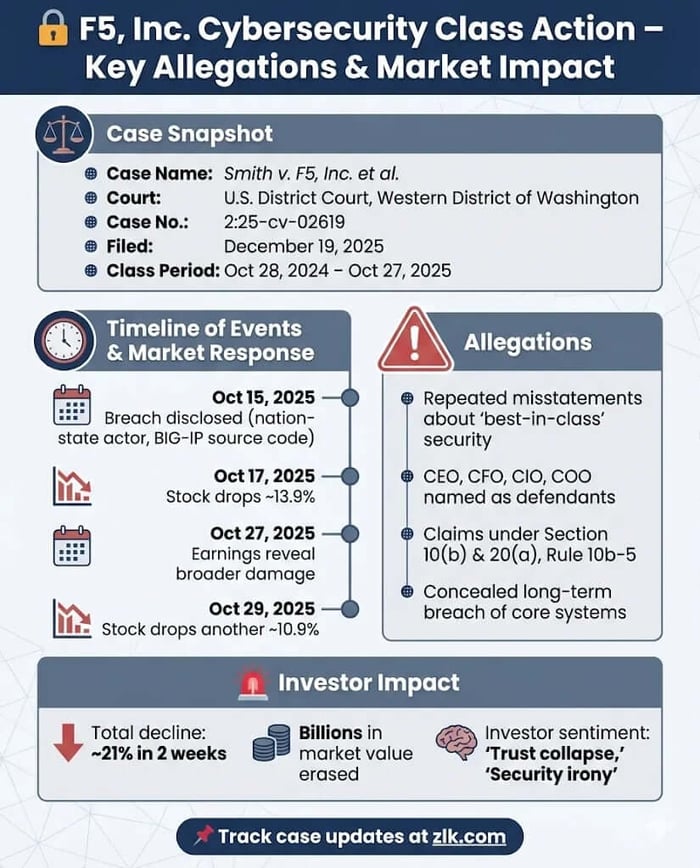
Case Name: Smith v. F5, Inc. et al.
Case No.: 2:25-cv-02619
Jurisdiction: U.S. District Court, Western District of Washington at Seattle
Filed on: December 19, 2025
Class Period: October 28, 2024-October 27, 2025
Introduction
F5, Inc. told investors it was winning the cybersecurity arms race. According to shareholders, it wasn’t even securing itself.
On December 19, 2025, a federal securities class action was filed in the U.S. District Court for the Western District of Washington against F5, Inc. and senior executives, alleging that the company misled investors about the strength of its cybersecurity capabilities while concealing a long-running breach of its most important product development environment. The lawsuit claims that repeated assurances about “best-in-class” security inflated F5’s stock price—until reality surfaced in a pair of disclosures that erased billions in market value.
Backdrop and Business Context
F5 is a global provider of application delivery and security products, best known for its BIG-IP platform, which manages and secures traffic for mission-critical enterprise applications across on-premises, cloud, and hybrid environments. BIG-IP is not a side business. According to the complaint, it is F5’s highest-revenue product line.
During the class period, F5 positioned itself as a security-first company reinvented for the hybrid multicloud era. Executives repeatedly described a transformation—from legacy hardware vendor to indispensable security and software platform—framing cybersecurity not merely as a feature, but as the company’s competitive identity.
That identity mattered. Security credibility was the narrative engine driving renewals, expansion, and AI-related growth expectations.
Promises Made vs. Reality
Across earnings calls, analyst conferences, and investor presentations, F5 executives spoke with near-absolute confidence. On January 28, 2025, Locoh-Donou described F5 as delivering “the most effective and comprehensive application and API security platform in the industry.” On April 28, 2025 he repeated this message, saying during Q&A, "we happen to have the best technology in the industry to move data security and at real speed for customers." At a Goldman Sachs Conference on September 9, 2025, he stated that security and application performance are inseparable and that this "makes F5 absolutely critical to all application security.”
According to investors, those statements omitted a central fact: while these assurances were being made, a sophisticated threat actor had already established long-term, persistent access to F5’s BIG-IP product development and engineering systems, exfiltrating source code and vulnerability information.
The lawsuit alleges that the breach began months before it was disclosed—and that F5 continued to promote its security superiority while knowing its own defenses had failed.
Timeline of Alleged Misconduct and Disclosures
The class period begins October 28, 2024, following earnings statements touting F5’s security leadership.
Throughout late 2024 and 2025, executives reiterated the same theme: security was F5’s differentiator, renewal engine, and growth driver—particularly as AI adoption accelerated.
On October 15, 2025, the narrative cracked. F5 disclosed, via press release and Form 8-K, that a “highly sophisticated nation-state threat actor” had maintained persistent access to its systems, including BIG-IP source code. The company stated it was still assessing the impact.
The market reacted immediately. Over two trading days, F5’s stock fell approximately 13.9%.
Twelve days later, on October 27, 2025, the fuller picture emerged during F5’s fourth-quarter earnings release. Management revealed reduced growth expectations for fiscal 2026, citing elongated sales cycles, disrupted renewals, and increased remediation costs tied to the breach. BIG-IP’s centrality to revenue was also emphasized—magnifying the perceived damage.
Shares fell again, dropping an additional 10.9% in two days.
Investor Harm and Market Reaction
Together, the October disclosures erased more than 20% of F5’s market value in less than two weeks.
Investors allege that these losses were not the result of unforeseeable cyber risk, but of delayed truth. According to the complaint, had the breach and its scope been disclosed earlier—or had F5 moderated its security claims—investors could have priced risk accurately.
Instead, shareholders say they bought at artificially inflated prices, anchored to assurances that proved hollow once tested.
Litigation and Procedural Posture
The lawsuit asserts claims under Sections 10(b) and 20(a) of the Securities Exchange Act and Rule 10b-5.
Defendants include F5 and four senior executives: the CEO, CFO, Chief Innovation Officer, and COO. The complaint alleges scienter based on the magnitude of the breach, the timing of internal discovery versus public disclosure, and the centrality of security to F5’s business model.
Plaintiffs contend that the alleged misstatements were not peripheral optimism, but core representations about the company’s defining capability.
The case is in its early stages. No motion to dismiss has yet been adjudicated.
Shareholder Sentiment
Investor reaction to the October 2025 disclosures was one of shock, betrayal, and eroded trust, with many expressing outrage over the irony of a leading cybersecurity provider suffering a prolonged nation-state breach.
On X (formerly Twitter), users highlighted the severity, noting the hackers' access lasted at least 12 months and involved theft of BIG-IP source code, prompting comparisons to high-profile incidents and concerns about national security implications.
Discussions emphasized the delayed disclosure—F5 learned of the intrusion in August but announced it in October at government request—fueling accusations of poor governance and questions about how long attackers went undetected.
Retail investors on platforms like Stocktwits and Reddit described a "credibility collapse," with frustration centered on management's prior boasts of "best-in-class" security now ringing hollow. Post-earnings sentiment shifted toward long-term reputational damage, disrupted renewals, and whether trust in leadership could be restored, amplifying concerns about sustained pressure on bookings and valuations.
This visceral backlash contributed to the sharp stock declines, reflecting a broader investor view that the breach exposed not just technical vulnerabilities, but a fundamental mismatch between F5's security narrative and reality.
Analyst Commentary
Sell-side analysts responded to the October 2025 disclosures with caution and downgrades, highlighting heightened uncertainty around long-term customer trust, competitive positioning, and the potential for prolonged impacts from stolen BIG-IP source code and undisclosed vulnerabilities.
Following the earnings release and lowered FY2026 guidance (0-4% revenue growth vs. consensus ~4.8%), analysts noted that the breach could enable competitors to capitalize on disrupted renewals and new deals, eroding F5's market leadership in application security.
Needham downgraded FFIV from Buy to Hold, citing the network security breach and deal delays as key pressures on near-term growth despite strong Q4 results.
Seeking Alpha contributors maintained Hold ratings, emphasizing a "trust deficit" and significant reputational damage that could layer onto operational disruptions, with "unknown unknowns" from the nation-state actor's access persisting well into 2026.
Broader commentary drew parallels to past supply-chain incidents, underscoring that while no immediate exploitation was evident, the theft of source code introduced new valuation risks tied to customer behavior and sustained margin pressure.
SEC Filings & Risk Factors
F5’s Form 8-K disclosed the breach and cited government-approved delay in public reporting. At the time, the company stated it had not yet determined a material financial impact.
The subsequent earnings release contradicted that uncertainty, revealing lowered revenue guidance, margin pressure, and near-term disruption tied directly to customer remediation efforts.
Investors allege that prior risk disclosures spoke in generalities about cybersecurity threats—without acknowledging that such a threat had already materialized.
Conclusion: Implications for Investors
This case is not about whether cyberattacks happen. They do.
It is about whether a company can repeatedly sell security as its defining strength while withholding the fact that its own defenses were compromised—then ask investors for patience once the truth surfaces.
For investors, the lesson is familiar but unforgiving: when a company’s valuation rests on trust, credibility is not a soft asset. It is the asset.
Now, shareholders are asking a court to decide whether F5 crossed that line.
Disclaimer: This shareholder alert is for informational purposes only and does not constitute legal advice. Consult a qualified attorney for personalized guidance. No specific outcomes are guaranteed.
![F5, Inc. (FFIV) Securities Class Action Lawsuit Update [December 22, 2025]](https://dropinblog.net/cdn-cgi/image/fit=scale-down,format=auto,width=700/34260815/files/featured/ffiv-alert-plus-banner.webp)


![Alexandria Real Estate Equities, Inc. (ARE) Securities Class Action Lawsuit Update [December 19, 2025]](https://dropinblog.net/cdn-cgi/image/fit=scale-down,format=auto,width=700/34260815/files/featured/are-alert-plus-banner.webp)
![Sprouts Farmers Market, Inc. (SFM) Securities Class Action Lawsuit Update [December 19, 2025]](https://dropinblog.net/cdn-cgi/image/fit=scale-down,format=auto,width=700/34260815/files/featured/sfm-alert-plus-banner.webp)
![PubMatic, Inc. (PUBM) Securities Class Action Lawsuit Update [November 27, 2025]](https://dropinblog.net/cdn-cgi/image/fit=scale-down,format=auto,width=700/34260815/files/featured/pubm-alert-plus-banner.webp)